At a Glance
- Solution type: Managed SOC (24x7 SIEM + SOAR + threat intel) for SMBs
- Platforms used: Wazuh SIEM, TheHive incident management, n8n SOAR, Cortex response, MISP threat intel
- Typical deployment time: 2-3 weeks from kickoff to live monitoring
- Engagement models: Managed SOC Service (we monitor) or SOC Implementation (we build, you operate)
- Reporting: 11 report templates, automated PDF and Excel delivery to your inbox
- Response time: instant, no delay. Architecture review starts same or next business day after scoping
What is a Managed SOC?
A Security Operations Center (SOC) is a dedicated team plus technology stack that monitors your IT infrastructure 24x7, detects threats, triages incidents and responds to attacks before they cause damage. A Managed SOC is the same capability delivered by an external provider, so you get round-the-clock security operations without hiring an in-house security team.
Codesecure delivers Managed SOC for SMBs using an open-source stack: Wazuh SIEM for log management and threat detection, TheHive for incident case management, n8n for SOAR automation, Cortex for response actions and MISP for threat intelligence. No license fees means we put your budget into deployment quality, tuning and 24x7 analyst coverage rather than into vendor licensing.
Why SMBs Need a SOC
Small and mid-size businesses are increasingly targeted by ransomware, phishing and data theft because attackers know SMBs lack dedicated security teams. The myth that "we are too small to be a target" is exactly what makes SMBs the easiest target. Indian SMBs in fintech, healthcare, manufacturing and SaaS are seeing record breach activity in 2024-26.
SOC is also rapidly becoming compliance baseline. RBI Cyber Security Framework requires 24x7 monitoring for regulated entities. DPDP Act 2023 expects reasonable security safeguards including incident detection and response. ISO 27001 Annex A.8.15-A.8.16 mandates logging and monitoring. SOC 2 Common Criteria CC7 requires evidence of continuous monitoring. Without a SOC, both attackers and auditors find the gap.
Our SOC Stack: Open-Source, Enterprise-Grade
Each tool in our stack is chosen for reliability, transparency and real-world effectiveness. Together they cover the full SOC lifecycle from log collection to threat hunting:
Wazuh SIEMLog collection, threat detection, FIM, vulnerability monitoring
TheHiveIncident case management with full audit trail
n8n SOARAutomated playbooks for triage and containment
CortexAutomated response, IOC enrichment, analyzer integration
MISPThreat intelligence feeds and IOC correlation
What's Included
Every Managed SOC engagement includes the full operational lifecycle:
24x7 Threat DetectionWazuh agents on endpoints, servers, network devices, cloud workloads
Incident Case ManagementTheHive case workflows with named-analyst assignment and SLAs
SOAR Automationn8n playbooks for repetitive triage, IOC enrichment, containment
Threat IntelligenceMISP-curated IOC feeds matched against your environment
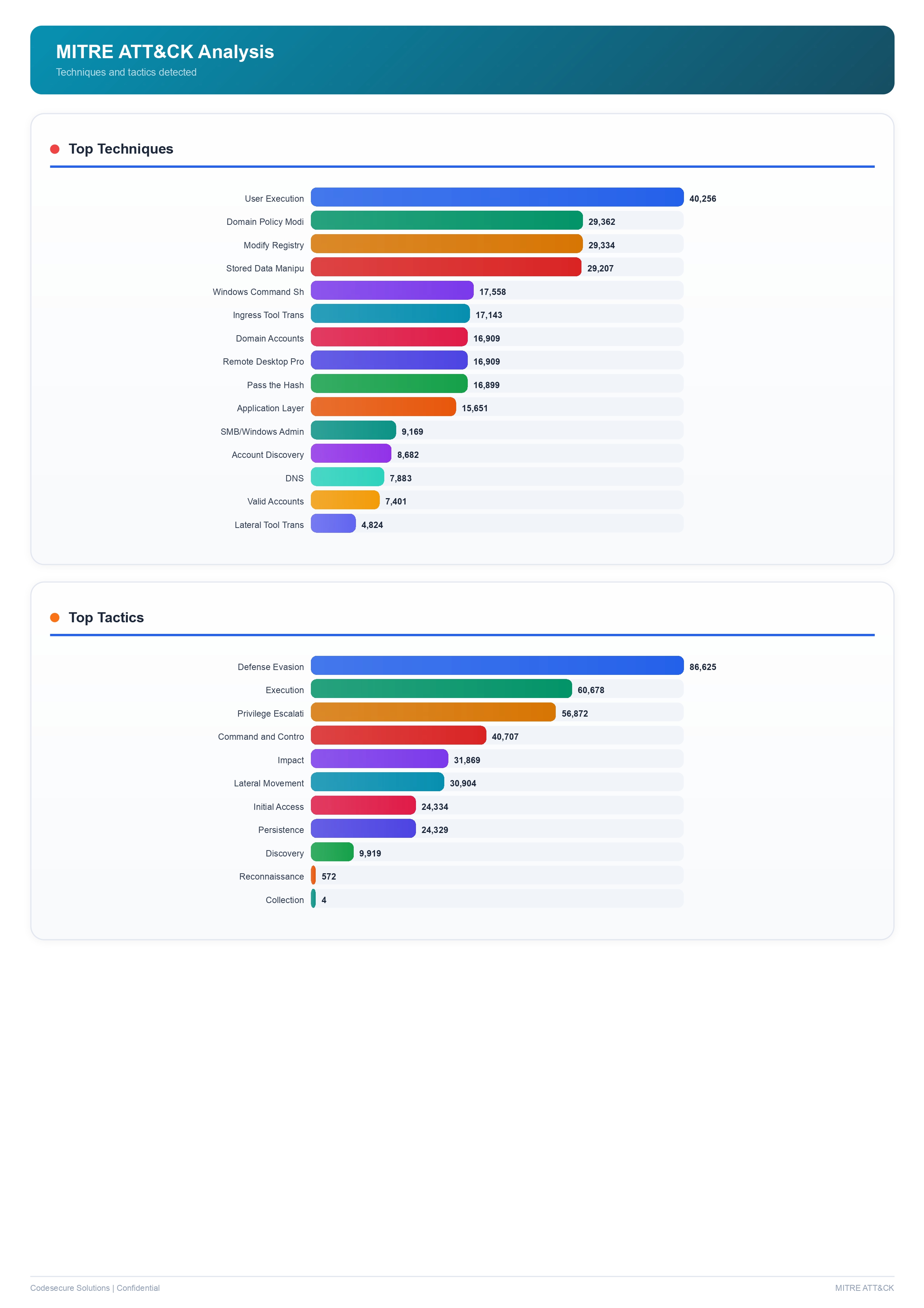
MITRE ATT&CK Coverage30-50 detection rules mapped to ATT&CK techniques
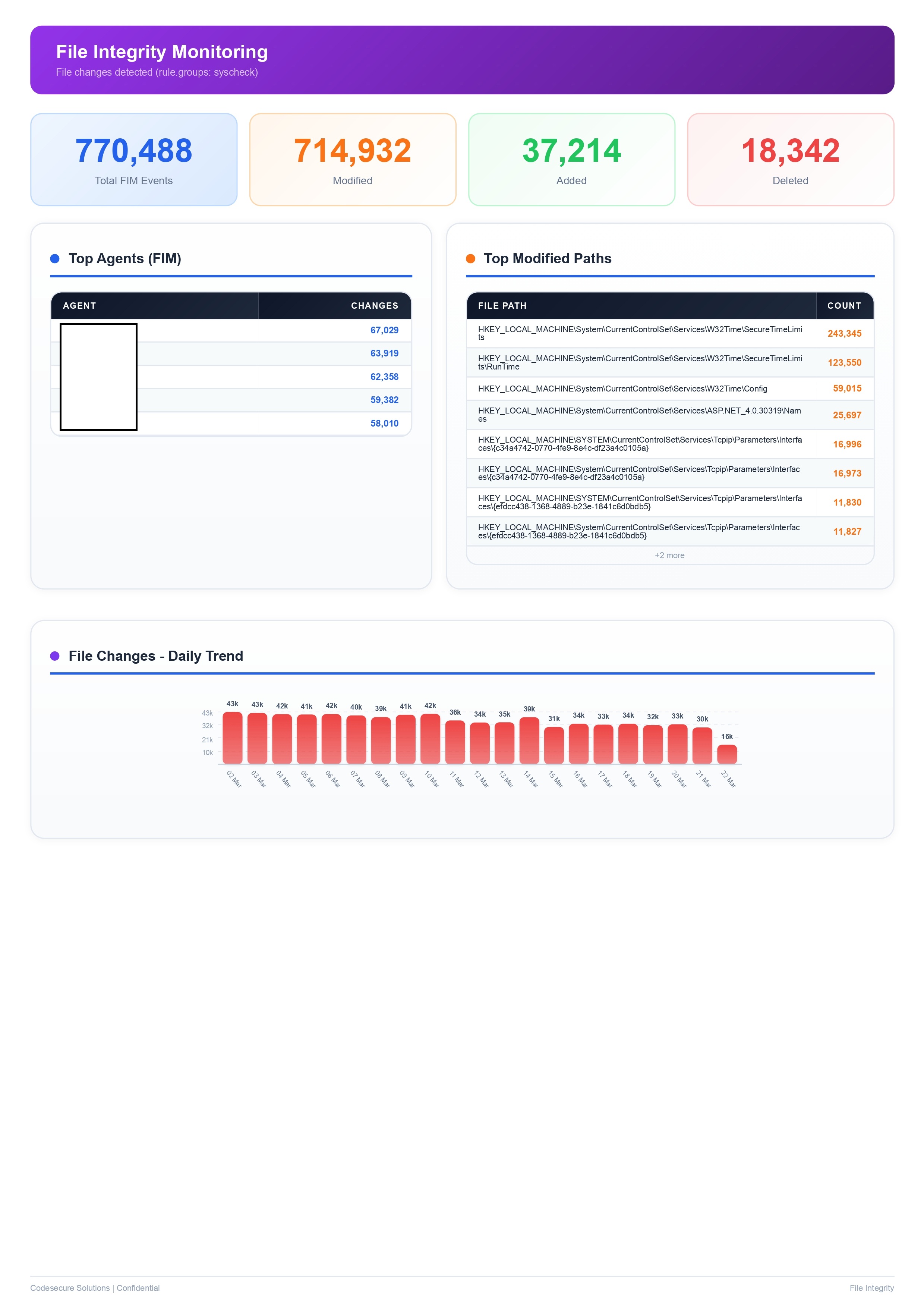
File Integrity MonitoringReal-time detection of unauthorised changes to critical files
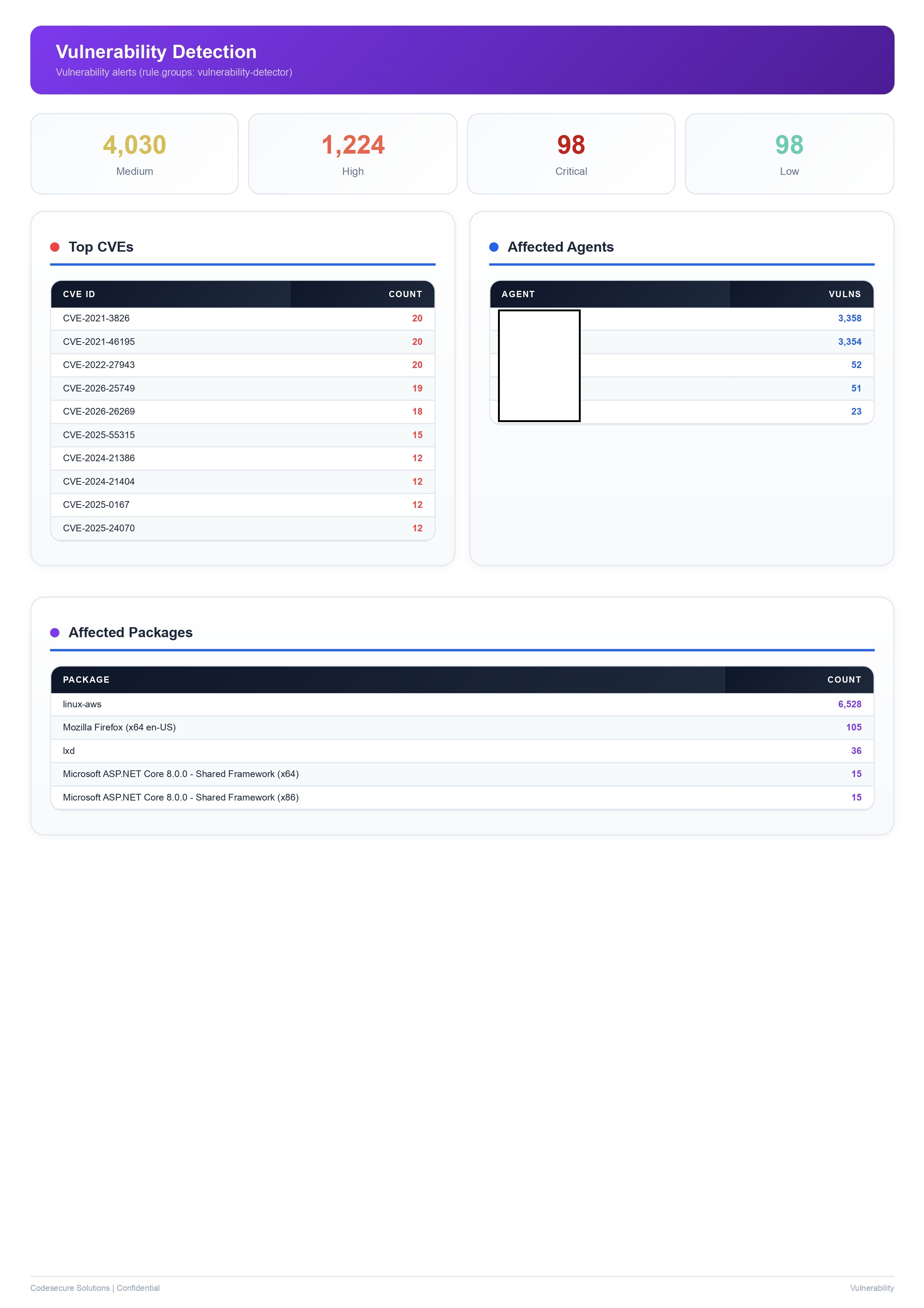
Vulnerability DetectionContinuous CVE matching against installed software on agents
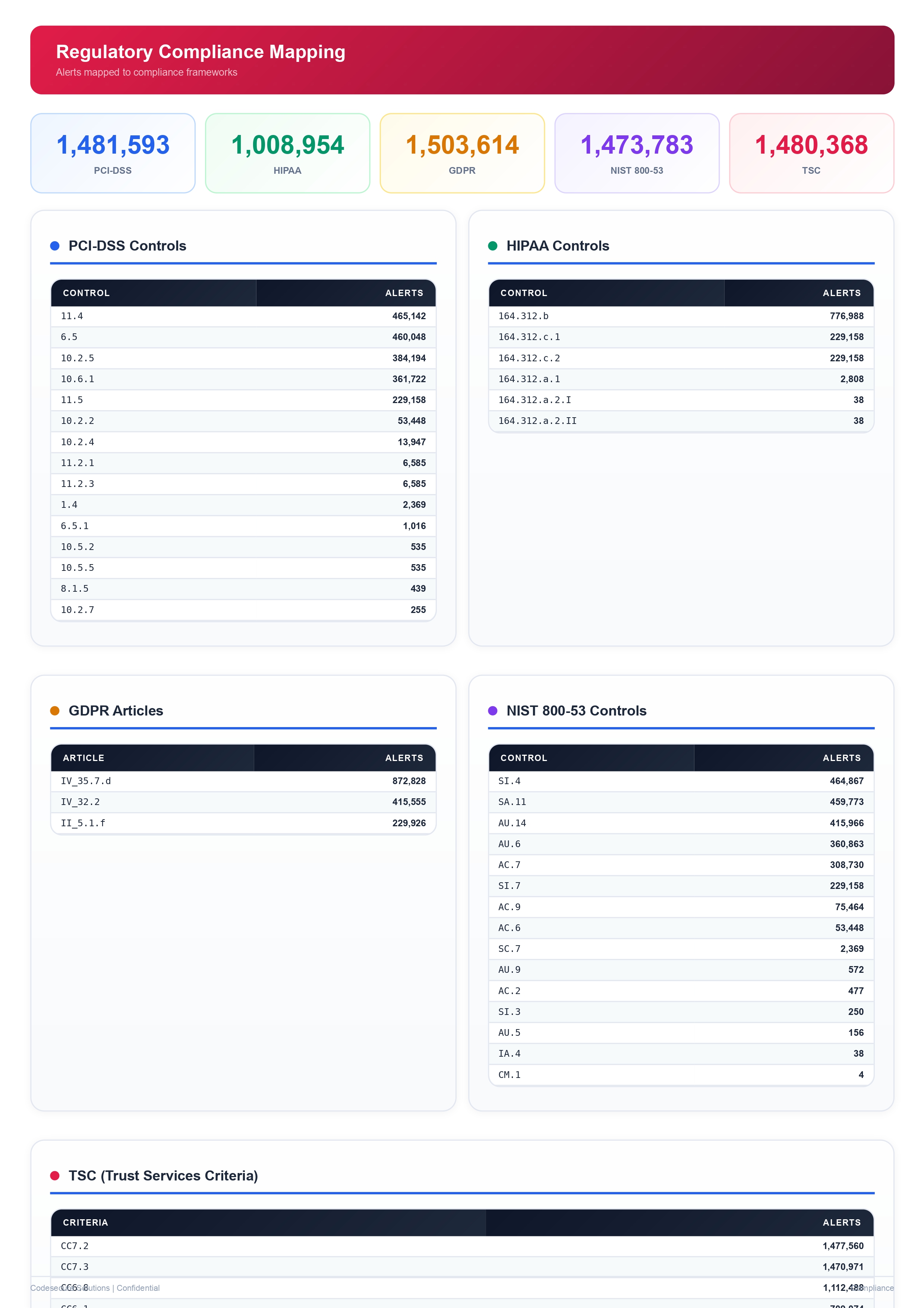
Compliance Audit LoggingISO 27001, PCI DSS, HIPAA, DPDP-aligned audit evidence
11 Report TemplatesDaily, Weekly, Monthly, Compliance, MITRE, IR and more
Monthly Review CallsNamed analyst reviews metrics, incidents and tuning with your team
Built-in Security Report Engine
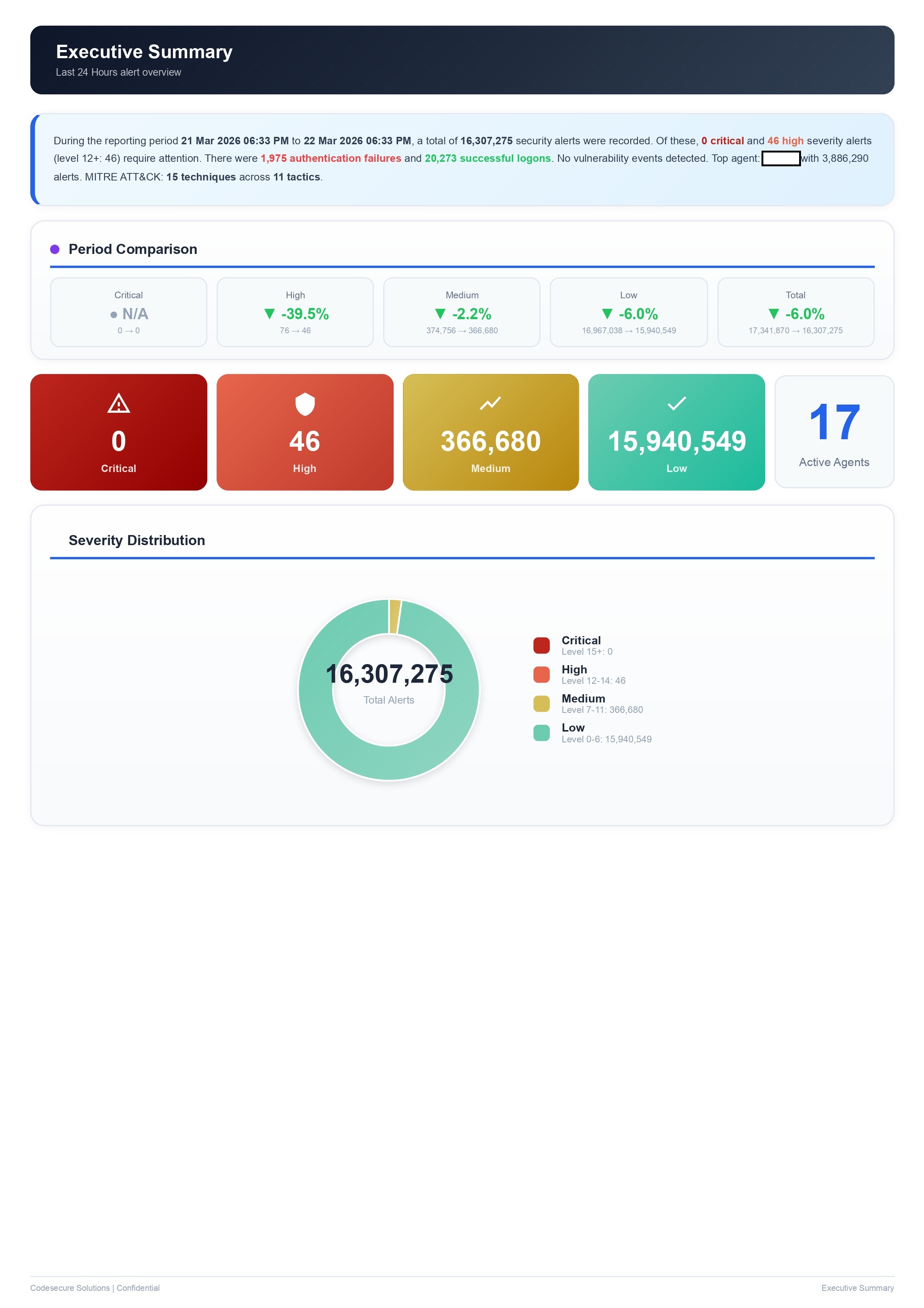
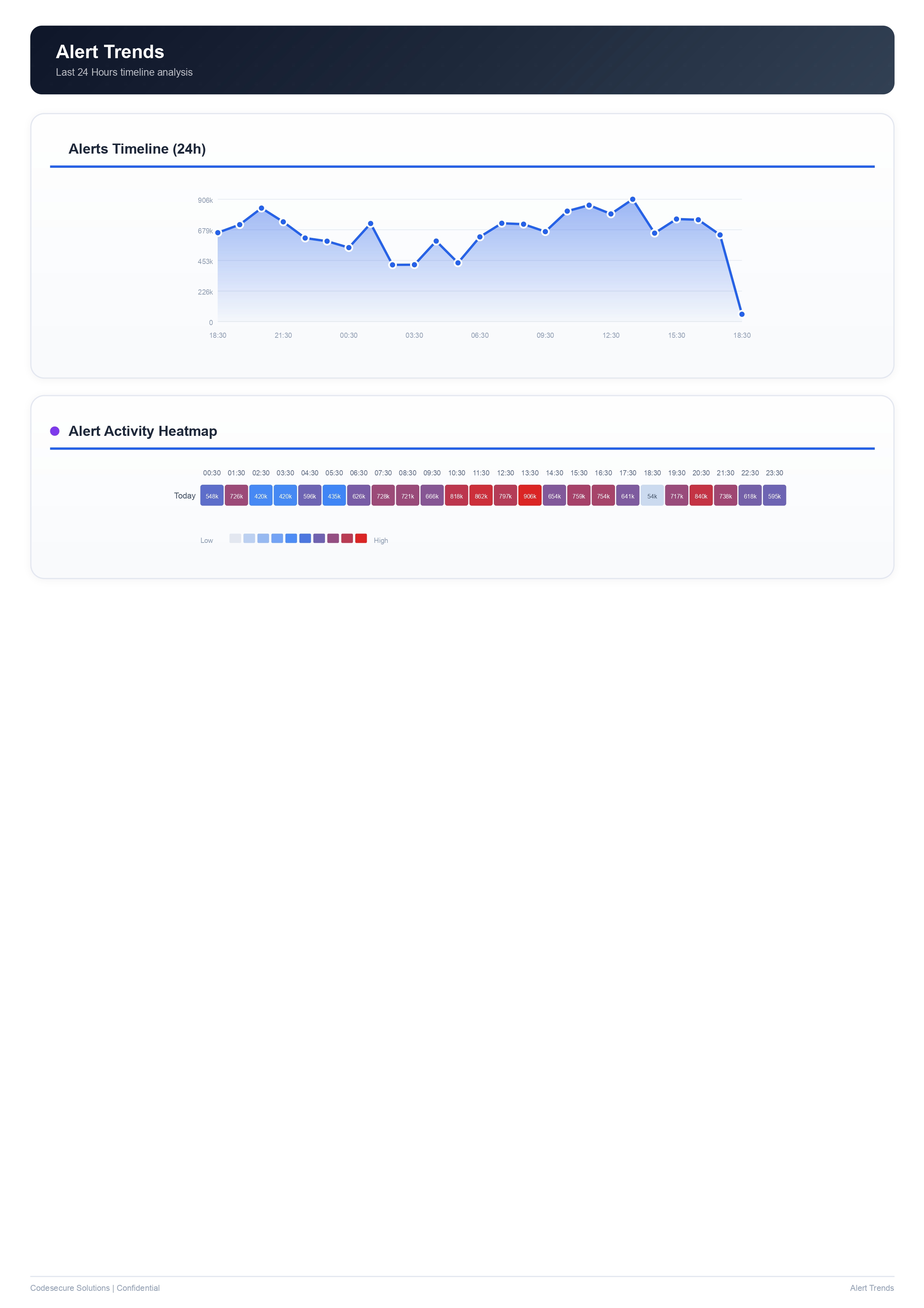
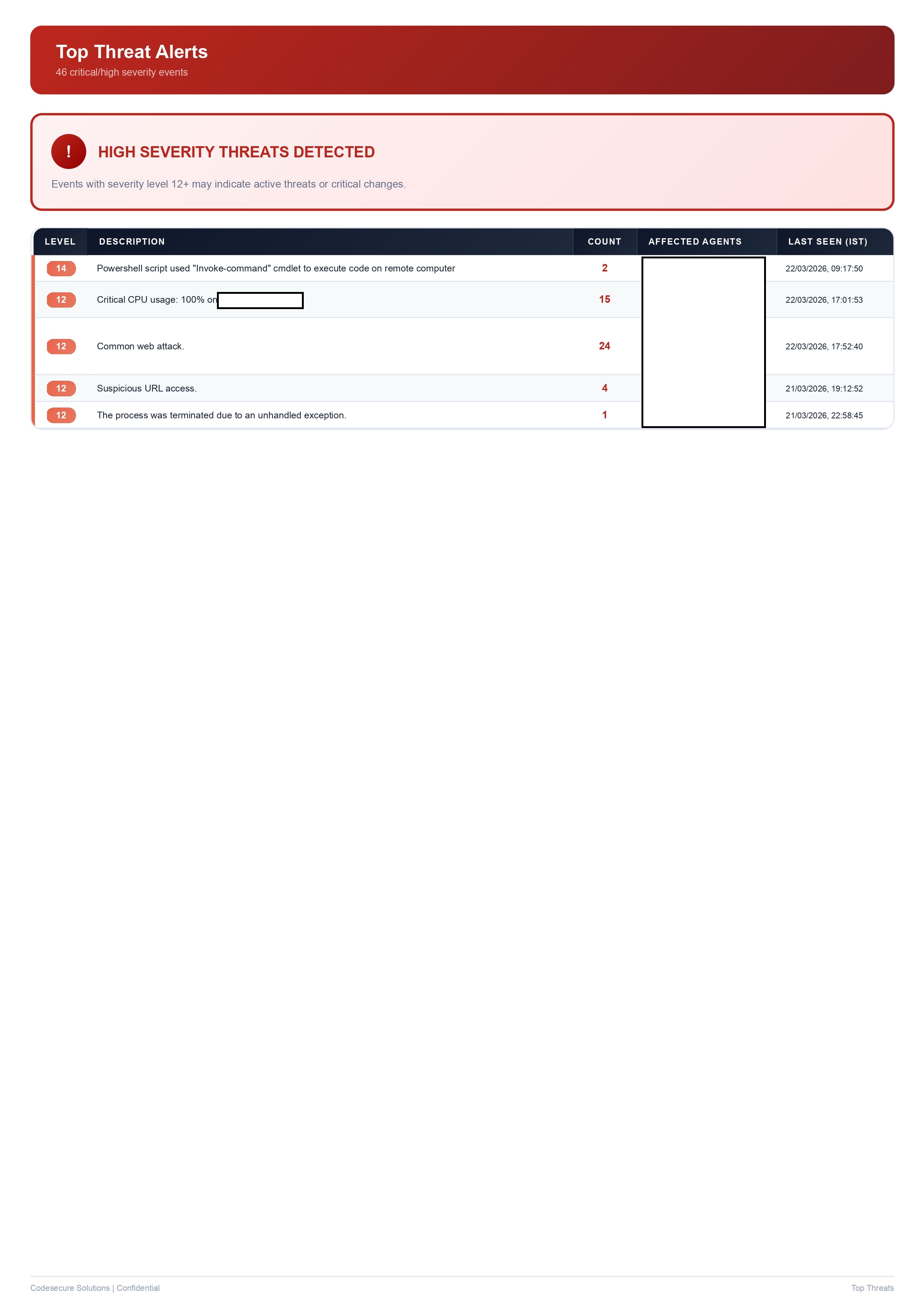
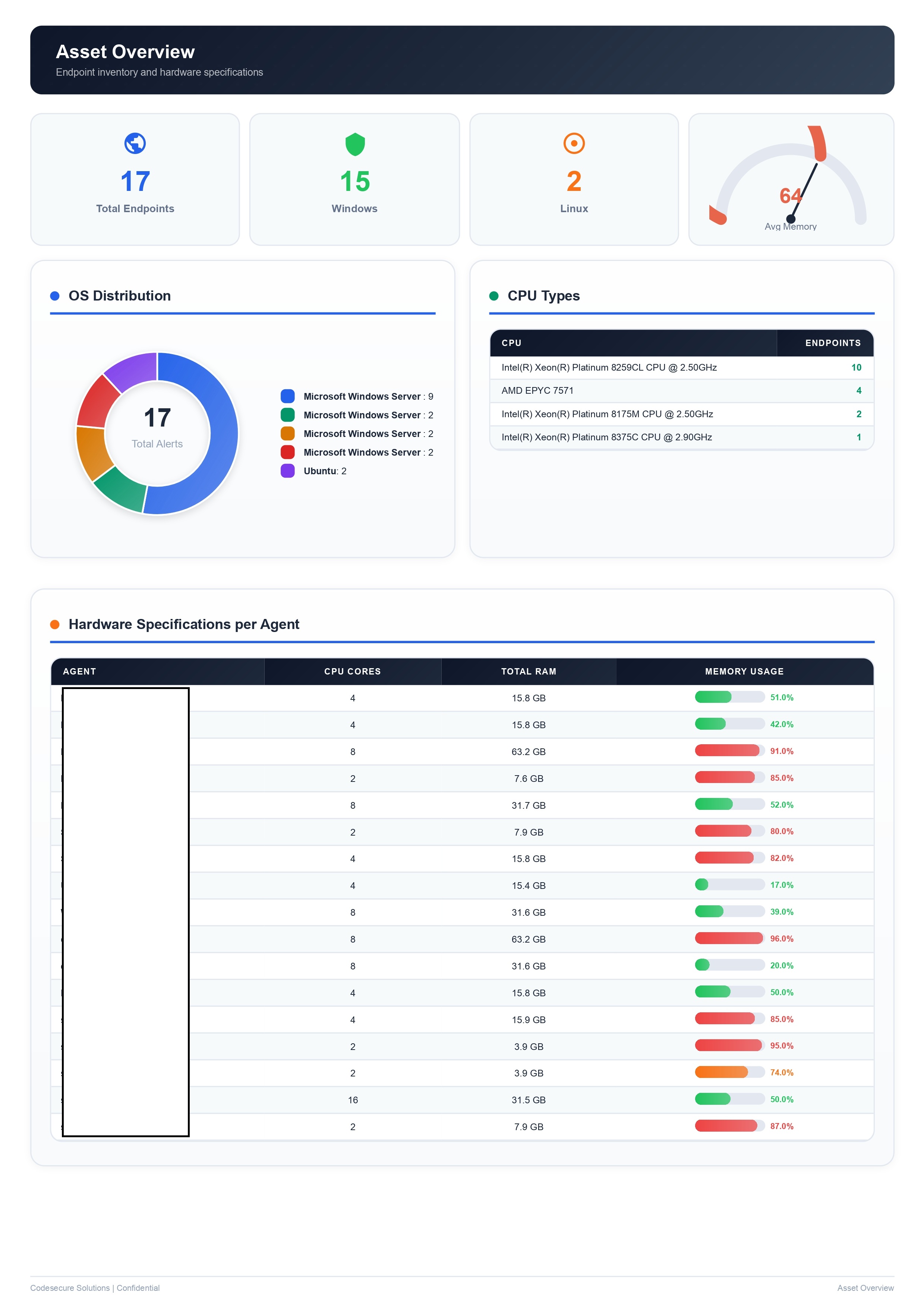
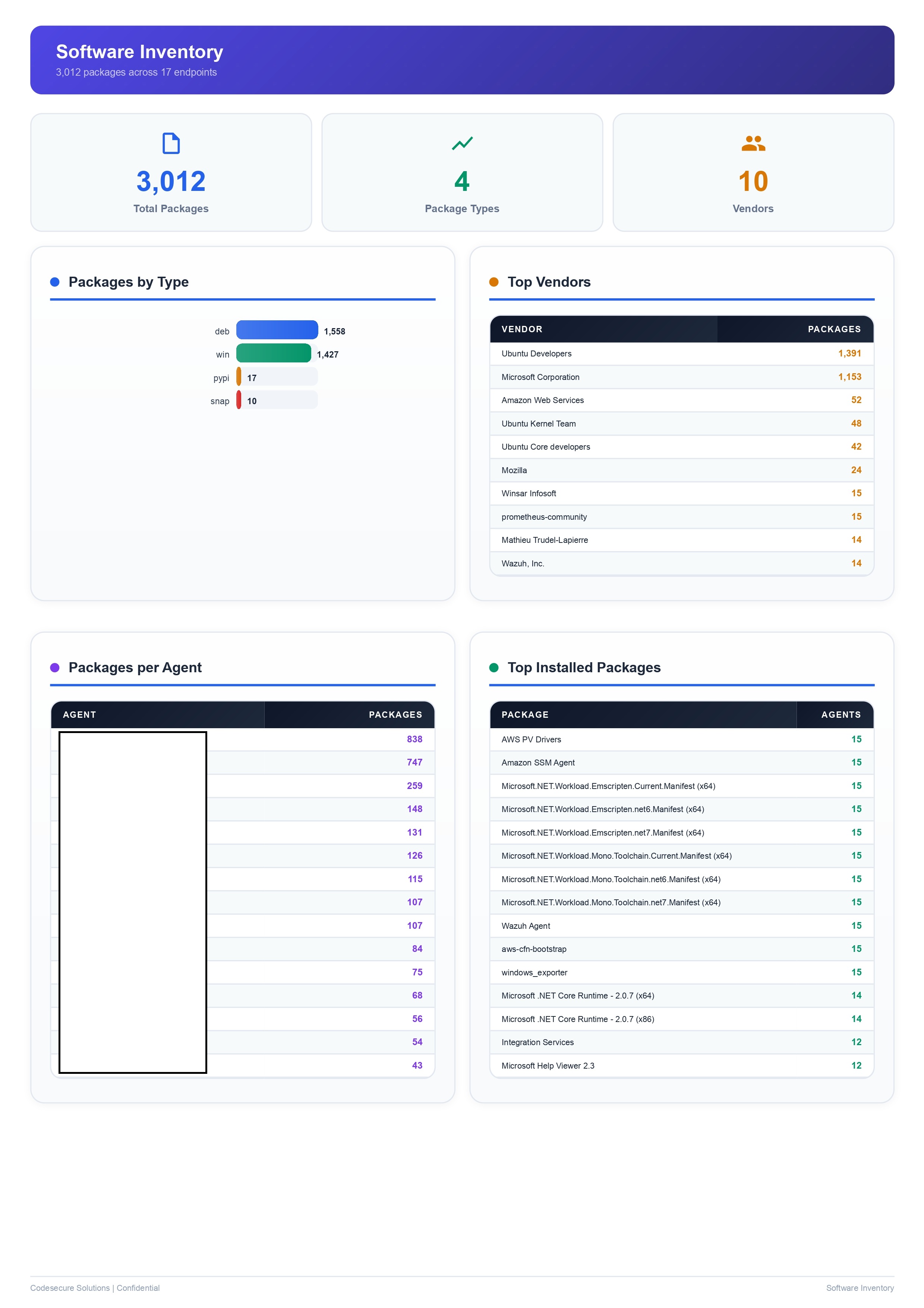
Wazuh does not have a native report module. We built our own. The Codesecure Report Engine generates 11 professional PDF and Excel reports automatically, ready to share with your team, management or auditors. Every report is branded with your company name and delivered to your inbox on a schedule you control. Click any thumbnail to view full size, then use the arrows to navigate through the report pages.
See a Sample Report Pack
Request our sample reports: daily, weekly, monthly, MITRE and compliance, anonymised real outputs. Instant response, no delay.
Request Sample Reports
Choose the Right Engagement Model
Both models deliver the same SOC stack and 11-template reporting engine. The difference is who operates it day-to-day:
Most Popular
Managed SOC Service
We monitor. You stay protected.
- We deploy and configure the full SOC stack on your infrastructure or cloud
- Our analysts monitor alerts 24x7 on your behalf
- Automated SOAR playbooks for immediate response
- Scheduled PDF reports delivered to your inbox
- Monthly review calls with your team
- No need to hire in-house security staff
- Best for: SMBs without a dedicated IT security team
SOC Implementation
We build it. You run it.
- We deploy and configure the full SOC stack on your servers
- Your team is trained on operating Wazuh, TheHive and n8n
- Detection rules, playbooks and runbooks handed over
- Optional retainer for tuning, upgrades and incident escalation
- You retain full control and data sovereignty
- Best for: teams with in-house IT capability who want to operate SOC themselves
How Our Managed SOC Works
From deployment to daily monitoring, here is the end-to-end flow:
1
Deployment & Agent Setup
Wazuh manager deployed on your infrastructure or cloud. Agents installed on endpoints, servers and cloud workloads. Network device log forwarding configured.
2
Continuous Monitoring
24x7 log ingestion, normalisation and correlation. Detection rules mapped to MITRE ATT&CK and your threat profile fire alerts in real time.
3
Automated Triage
n8n SOAR playbooks enrich alerts with MISP threat intel and Cortex analyzers. Low-confidence alerts auto-closed, high-confidence escalated to TheHive cases.
4
Incident Response
Named analyst takes ownership of escalated cases. Containment per pre-approved playbooks: isolate host, block IOC, disable account, notify your team.
5
Automated Reporting
Report engine generates 11 PDF and Excel reports on schedule. Daily, weekly, monthly cadences plus ad-hoc compliance and incident reports.
6
Monthly Review & Tuning
Monthly call covers metrics, incident trends, tuning needs, new detection coverage. Quarterly ATT&CK coverage gap analysis.
Industries We Serve
Our managed SOC fits any growing business handling sensitive or regulated data:
Fintech & BFSI
Healthcare
Manufacturing
SaaS & IT Services
E-commerce & Retail
Logistics & Supply Chain
Education & EdTech
Maritime & Shipping
Legal & Professional Services
Deployment Timeline
Most SMB SOC deployments reach live monitoring within 2-3 weeks. Instant response, no delay, we start architecture review same day or next business day after scoping.
Week 1
Architecture & Deploy
Scoping call, NDA, sizing, Wazuh manager + TheHive + n8n + Cortex + MISP deployed on your infra or cloud.
Week 2
Agent Rollout & Tuning
Agents installed on endpoints, servers, cloud workloads. Detection rules tuned to your environment. SOAR playbooks live.
Week 3
Go-Live & Reports
24x7 monitoring handoff to named analyst team. Report engine schedules configured. First weekly and monthly report delivered.
// Platforms & Tools We Support
Wazuh SIEM
TheHive
n8n SOAR
Cortex
MISP
Elasticsearch
OpenSearch
Filebeat / Auditbeat
Suricata
MITRE ATT&CK
VirusTotal
AbuseIPDB
Talk to a SOC Lead
30-minute call with our SOC engineering lead. Get a sense of fit, scoping and timeline with no sales pressure.
Schedule Free Call
Frequently Asked Questions
What is a Managed SOC and do small businesses really need one?
A Managed Security Operations Center (SOC) is a dedicated team and technology stack that monitors your IT infrastructure 24x7 for threats, detects incidents, and responds to them. Small and mid-size businesses are increasingly targeted by ransomware, phishing and data theft precisely because attackers know they lack dedicated security teams. A managed SOC gives you continuous protection without the cost of hiring in-house analysts, and is increasingly expected by enterprise customers, insurers and regulators.
Why do you use Wazuh instead of commercial SIEM tools?
Wazuh is a professional-grade open-source SIEM and XDR platform trusted by thousands of organisations globally. Commercial alternatives carry significant per-GB and per-endpoint licensing that puts professional SOC out of reach for SMBs. Wazuh delivers log management, threat detection, file integrity monitoring, vulnerability detection and compliance reporting with zero license fee, which lets us put more budget into deployment, tuning and 24x7 analyst coverage. We are deeply familiar with Wazuh, ELK, OpenSearch and OSSEC, that is our SIEM specialisation.
What kind of reports do you generate and how often?
11 report types: Daily Security Summary, Weekly Security Report, Monthly Executive Report, MITRE ATT&CK Report, Compliance Report, Incident Response Documentation, IT Asset Inventory, Authentication Audit, Vulnerability Assessment, Agent Health Report, File Integrity Monitoring Report. Reports are PDF and Excel, generated automatically on schedule, and delivered to your inbox. Ad-hoc on-demand reports are also available.
What is the difference between Managed SOC and SOC Implementation?
Managed SOC: we deploy the full stack on your infrastructure and our team monitors, responds and reports on your behalf on an ongoing basis. SOC Implementation: we deploy and configure the complete stack on your servers, train your team and hand it over for you to run internally, with optional retainer for tuning and escalation. Both options include the full reporting engine.
Is my data stored on your servers or on my own infrastructure?
For both engagement models, the SOC stack is deployed on your own servers or your preferred cloud environment. Your log data, security events and reports stay within your infrastructure. We do not store your security data on our servers. This gives you full data sovereignty and makes compliance with DPDP Act 2023, ISO 27001 and sector-specific regulations easier to demonstrate.
How quickly can you start?
Instant response, no delay. We respond within an hour during business hours, send a fixed-scope proposal in 24-48 hours under signed NDA, and start architecture review the same day or next business day after sign-off.
Can SOC evidence satisfy ISO 27001, PCI DSS, RBI or DPDP audits?
Yes. Our managed SOC directly supports ISO 27001 Annex A.8.15-A.8.16 (logging and monitoring), A.5.24-A.5.28 (incident management), PCI DSS Requirement 10 (log management), SOC 2 Common Criteria CC7 (system monitoring) and RBI Cyber Security Framework SOC requirements. The compliance report template produces audit-ready evidence aligned to each framework.
Ready to Set Up a SOC for Your Business?
Codesecure delivers professional Managed SOC for SMBs with the Wazuh + TheHive + n8n + Cortex + MISP stack, 24x7 analyst coverage and the built-in 11-template reporting engine. Free 30-minute consultation, instant response, no obligation.
Get a Free SOC Consultation
See All Solutions